What a Sheriff's Office Hack Reveals About Your Facebook Security
Facebook is the most targeted social media platform on the planet. With over 2 billion monthly active users, 1 in 5 social media accounts face hacking attempts annually (according to Cropink). As a result, every month, roughly 67,0940 users search Google for help recovering a hacked Facebook account.
If your business relies on Facebook to connect with customers or share updates, this should be a wake-up call. You need to do everything in your power to protect your accounts and reduce your attack surface.
In this post, we'll break down a recent Facebook Page hack that targeted a law enforcement agency, explain why it matters for your business, and walk you through 7 warning signs that your Facebook Page could be next.
What Happened to the Wood County Sheriff's Office Facebook Page?

On Wednesday, February 4, 2026, the Wood County Sheriff's Office released a statement saying its Facebook page had been hacked. Hackers took control of the page and published unauthorized posts that had nothing to do with the department.
Their official public statement read, "The Wood County Sheriff's Office facebook page has been hacked, we are aware and attempting to resolve the issue. We apologize for any compromised posts that have occurred on the page last evening that were not done by our office."
This isn't the first cybersecurity incident involving Wood County. According to The Morning Show BG, county computer systems were hit by a ransomware attack in December 2024. In that incident, county commissioners agreed to pay a $1.5 million ransom.
On Thursday, the Wood County Sheriff's Office regained control of their Facebook page. According to a post on the page, "Effective just before 12:00 p.m. on Thursday, February 5, 2026, with the assistance of Meta, the Wood County Sheriff's Office Facebook page has been restored and no longer compromised. Posts that were made under whomever took control of the page were removed."
Sheriff Mark Wasylyshyn stated, "We are extremely fortunate to have a local connection with Meta, who helped escalate to gain control over our page again and can resume our normal social media engagements on our page without having to rebuild and start from scratch. Our detectives are still investigating to see if it's possible to find out who compromised our page."
Why Should Your Business Care About This?
Wood County was fortunate enough to have a direct contact at Meta who escalated their case and helped them recover their page in about 24 hours. However, that is not the reality for most people.
The vast majority of businesses and creators struggle to even get in contact with Meta when their accounts are compromised. Many never recover their accounts at all; they lose years of content, followers, and trust permanently. And Facebook being the most compromised social media platform only makes this risk greater.
That's why you need to be very careful with who you give access to your accounts and how strong your overall security posture is. You can't rely on having a connection at Meta to save you.
7 Warning Signs Your Facebook Page Could Be Hacked
The good news is that while you can't control whether someone will try to hack you, you can reduce your attack surface to make it much harder for hackers to breach your Facebook Page.
Here are seven warning signs to watch for:
1) You Use Weak Passwords
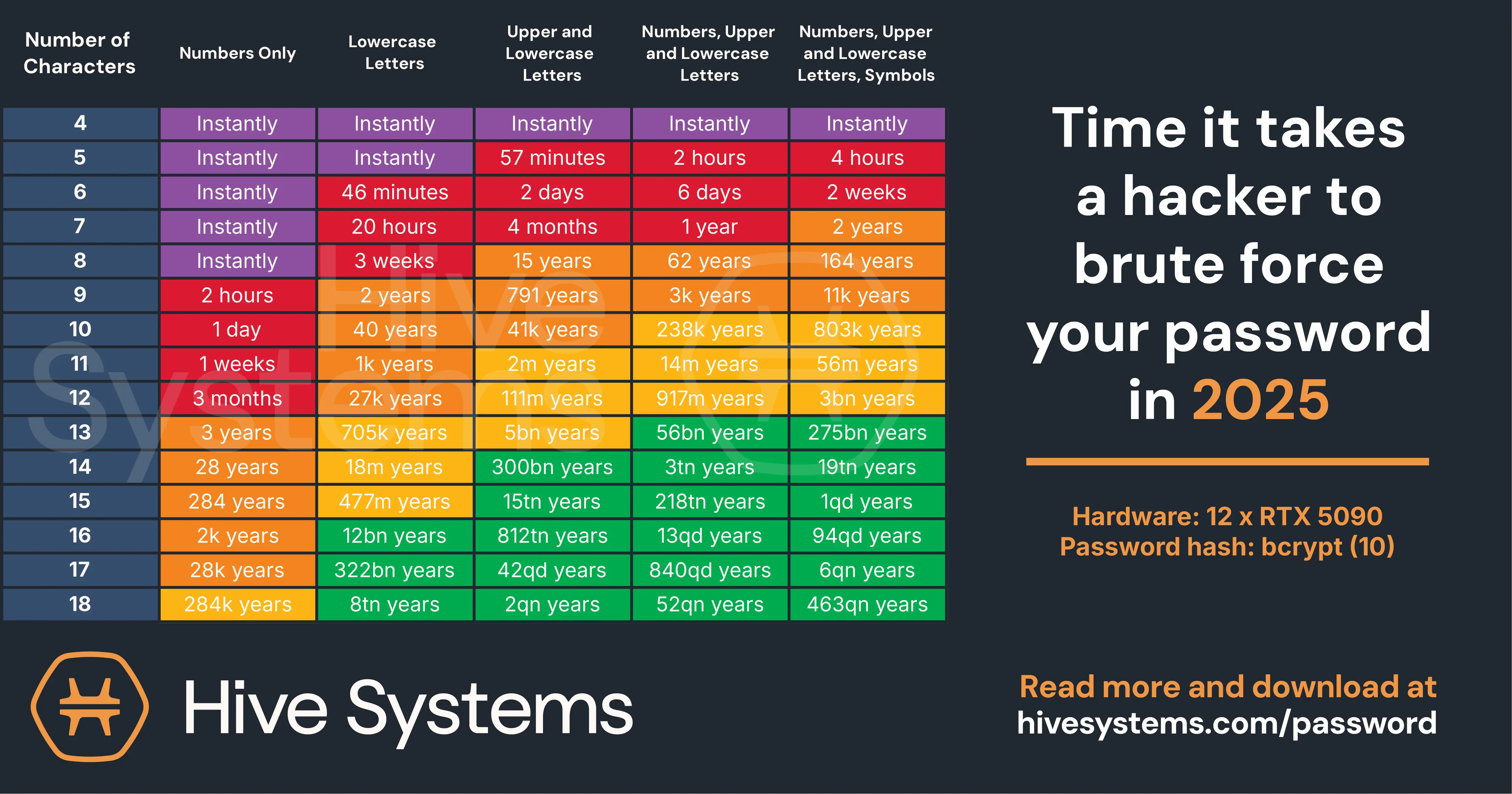
The main reason businesses get hacked is poor password strength and poor password management. According to Hive Systems' 2025 Password Table, an 8-character password made up of only numbers can be cracked instantly using modern hardware. As such, you have to make it as long and complex as possible to ensure maximum security.
That said, creating a strong password is easy. All you have to do is use between 16 and 20 characters, mix uppercase and lowercase letters with numbers and symbols, and never reuse passwords across accounts. Also, a 16-character passphrase made of random words is far harder to crack than a short, complex password.
If you think you won't remember all your different passwords, use a company-approved password manager like 1Password, Proton Pass, Bitwarden, or LastPass to securely create, store, and retrieve them.
2) You Don't Use 2FA
Two-factor authentication (2FA) is a security method that requires two forms of identification before granting access to an account. The way it works is simple: first, you enter your password and then confirm your identity through a second step, such as a code sent to your phone or generated by an authenticator app.
2FA is one of the best ways to prevent brute force attacks from succeeding. According to a Google security study, SMS-based 2FA blocks up to 100% of automated bot attacks, 96% of bulk phishing attacks, and 76% of targeted attacks. On-device prompts perform even better, blocking 100%, 99%, and 90% of those same attack types.
And while regular 2FA is fantastic for individual users, it creates a bottleneck for social media teams. Team members need to request access codes from an administrator every time they log in. For example, imagine a social media manager needs to post an urgent update at 7 AM, but the admin who controls the 2FA codes doesn't start work until 9 AM.
This can be avoided by using 2FA for teams. Regular 2FA sends codes to one person's device, 2FA for teams distributes authentication across authorized team members so multiple people can securely log in without waiting on a single point of contact.
3) You Don't Employ Best User Access Management (UAM) Practices
If someone leaves your organization, you must revoke their access to your Facebook Page immediately. Otherwise, if their personal account is compromised later, attackers could gain direct access to your business page. We've seen this happen many times, and many businesses never recover their accounts after an incident like this.
Follow UAM best practices by auditing who has access regularly, quickly removing inactive users, and assigning the minimum permissions each team member needs.
4) You Are Not Protecting Your Local Devices
One common way hackers breach social media profiles is by using info stealers to steal session cookies (allowing them to bypass your email, password, and 2FA entirely).
An info stealer is malware designed to extract sensitive data from your device, including saved passwords, browser cookies, and autofill information. They spread through phishing emails, malicious downloads, and compromised websites.
The best way to stop info stealers is to use antivirus software, which scans your device for malicious programs, blocks known threats in real time, and quarantines suspicious files before they can cause damage. That said, if you don't know which one to choose, we recommend Bitdefender. It's one of the best in the industry for stopping info stealers.
5) You Don't Actively Monitor Your Account for Suspicious Activity
A simple way to keep your accounts protected is to use social media monitoring: continuously tracking your account for unauthorized changes, suspicious login attempts, and other indicators of compromise. A monitoring tool scans your account around the clock and alerts you when something abnormal happens.
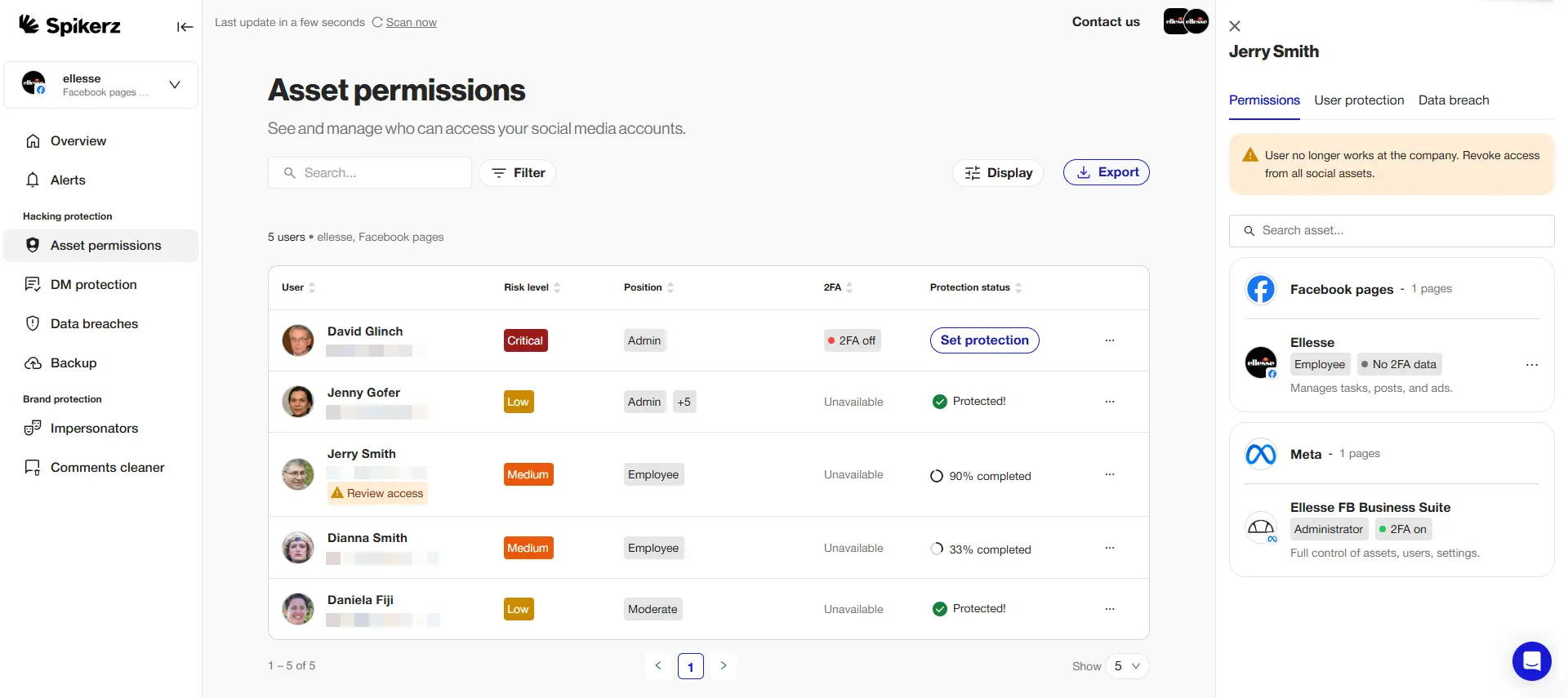
There are many monitoring tools on the market, so we recommend you choose one that focuses on security, like Spikerz.

Spikerz is a social media security platform designed to protect your accounts from a wide range of threats, like:
- Account takeover protection: Monitors your accounts 24/7 for unauthorized access and suspicious login activity, alerting you immediately so you can act fast.
- Impersonator takedown: Scans for fake accounts impersonating your brand so you can report them before they mislead your audience.
- Phishing protection: Detects phishing links and malicious messages targeting your profiles, stopping threats before they reach your team.
- Comment moderation: Filters harmful, spammy, and toxic comments from your posts, keeping your social media presence clean.
- Permissions management: Tracks who has access to your accounts, making it easy to revoke permissions when team members leave or roles change.
If you want to take your social media security to the next level, book a demo right now to see how Spikerz can help you secure your accounts.
6) You Don't Have a Social Media Policy
A social media policy is a documented set of guidelines that defines how your organization uses social media, who has access to accounts, and what security measures team members must follow. It helps onboard new team members into security practices and sets clear rules for using social media profiles.
A strong policy covers password requirements, 2FA protocols, content approval workflows, and crisis response procedures. Without one, your team is operating without guardrails.
If you want to easily create a social media policy, check out our editable social media policy template. It covers everything your organization needs: employee conduct, approval and escalation workflows, dedicated security requirements, and more. You'll also get an expert review from the Spikerz team to help spot security gaps and strengthen your policy.
7) You Don't Have a Rapid Response Team (RRT)
A rapid response team (RRT) is a designated group within your organization trained to act immediately when a security incident hits. Having an RRT reduces response time, minimizes damage, and ensures recovery steps are executed in the right order.
When the Wood County Sheriff's Office discovered their Facebook page had been hacked, they immediately contacted Meta, assigned detectives to investigate, and used their X account to communicate with the public. Because they had clear processes in place, they regained control within about 24 hours. Without those processes, they could have lost their page entirely, along with their nearly 9,000 followers.
So make sure to have an RRT in your organization. Define who is responsible for what, establish communication protocols, document your recovery process, and run practice drills so your team knows what to do when a real incident happens.
Conclusion
The Wood County Sheriff's Office hack is a clear reminder that no one is immune to social media threats. A law enforcement agency with cybersecurity awareness still had their Facebook Page taken over. Your business faces the same risk every day.
The difference between a minor inconvenience and a total account loss comes down to preparation. Strong passwords, 2FA for teams, user access management, device protection, active monitoring, a social media policy, and a rapid response team: these stand between you and a hacker who wants your account.
Don't wait for a hack to take action. Review your security setup today, close the gaps, and build the systems that will protect your business when it matters most.

