Cybersecurity Risk Management For Regulated Brands
Cybersecurity Risk Management For Regulated Brands
Did you know that the biggest challenge in cyber risk management is the growing gap between fast technological innovation and an increasingly fragmented global regulatory landscape?
AI tools are evolving faster than regulators can keep pace with, creating vulnerabilities that cybercriminals exploit daily. As a result, businesses face mounting pressure to protect their digital assets and meet compliance requirements that shift from one jurisdiction to the next.
So in this post, we'll break down what cyber risk management is, explore why it matters more than ever, and walk through the seven-step framework that helps regulated businesses protect their digital presence. Additionally, we’ll show you specific strategies to secure your most vulnerable attack surface: social media.
What Is Cyber Risk Management?
Cyber risk management is the process of identifying, analyzing, and responding to security threats that could damage your business's digital assets. It involves evaluating potential vulnerabilities in your systems, determining the likelihood and impact of attacks, and implementing controls to reduce those risks to acceptable levels.
The way this works is by continuously monitoring your digital environment for emerging threats while prioritizing protection efforts based on which assets matter most to your business. In other words, you assess each risk against your organization's tolerance levels, then decide whether to accept, transfer, mitigate, or eliminate specific threats.
The framework adapts as your business grows and threat landscapes shift, keeping your security posture aligned with real-world dangers.
Why Cyber Risk Management Matters
Cyberattacks like ransomware, data breaches, and phishing campaigns have exploded in recent years, forcing businesses to treat security as an operational priority. This is due to the financial and reputational damage caused from successful attacks that can destroy years of work in hours.
For example, according to Knowbe4's 2025 Phishing Threat Trends, from September 15, 2024, until February 15, 2025, they observed a 22.6% increase in ransomware payloads in phishing attacks (versus the previous six months).

The threat has become so significant that the 2024 Allianz Risk Barometer named cyber events the top global business risk.
What Are The Steps Of A Cybersecurity Risk Management Framework?
Cyberattacks aren't random events. If you know where to look, there are often clear signs of a planned attack against an organization. That said, it's difficult to evaluate cyber risk with total certainty.
Companies rarely have full visibility into cybercriminals' tactics, their own network vulnerabilities, or more unpredictable risks like severe weather and employee negligence. The good news is that there's an effective process that authorities like the National Institute of Standards and Technology (NIST) suggest companies follow.
Here’s how the risk management framework (RMF) works:
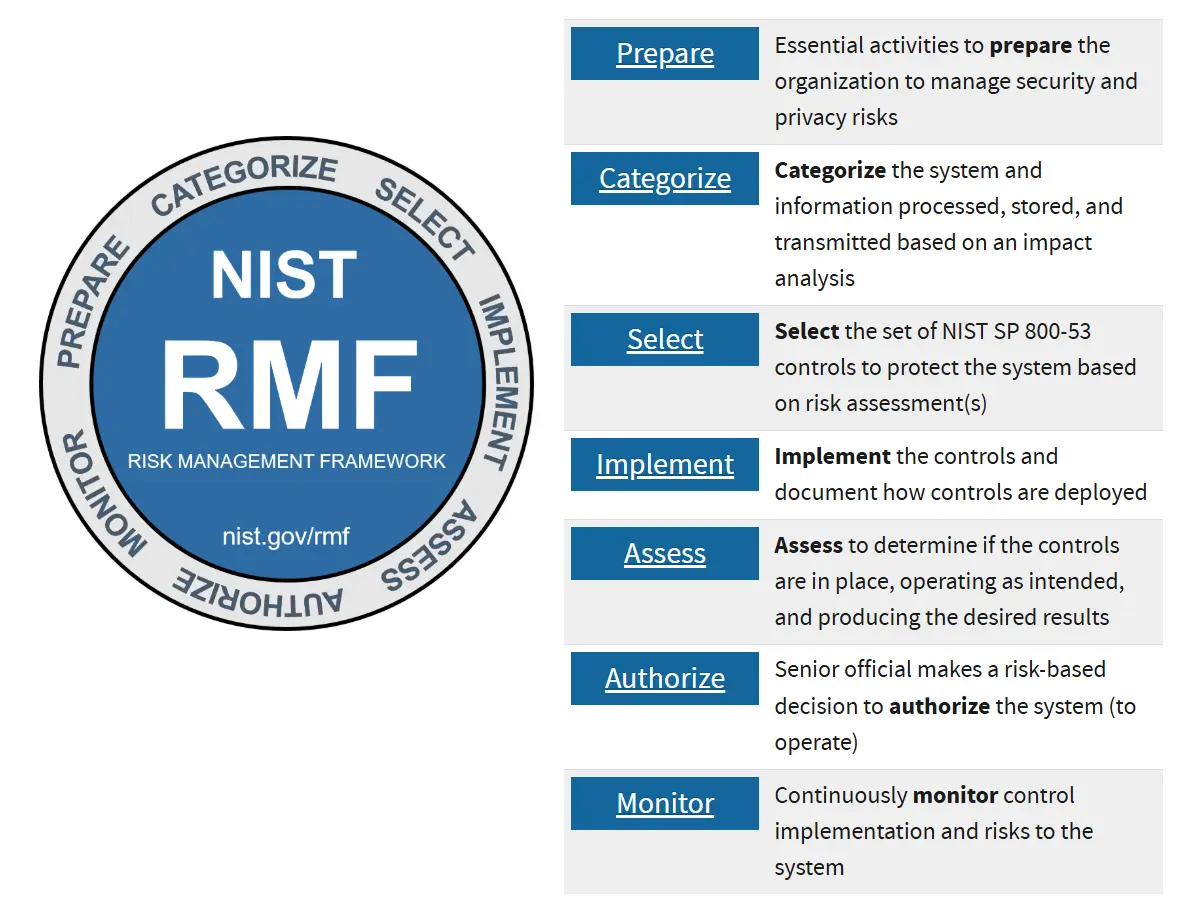
1) Prepare
This step establishes your organization's foundation for security by defining essential activities that help all levels of your company manage security and privacy risks. It also ensures everyone (from executives to frontline employees) understands their role in protecting your digital assets.
For example, your business should…
- Identify key risk management roles
- Establish an organizational risk management strategy and determine your risk tolerance
- Assess your organization-wide risk
- Create and implement an organization-wide strategy for continuous monitoring
- Identify common controls
2) Categorize
Categorization focuses on informing your risk management processes by determining the adverse impact with respect to the loss of confidentiality, integrity, and availability of systems and the information they process, store, and transmit.
You're essentially classifying how damaging it would be if different types of data were compromised. This classification drives every subsequent security decision you make.
During this step, your team…
- Documents system characteristics
- Completely categorizes the security of the system and information
- Reviews and approves decisions categorized by a senior leader
As a result, you create a shared understanding across your organization about which assets require the highest levels of protection and which systems need enhanced monitoring.
3) Select
Selection involves choosing, tailoring, and documenting the controls necessary to protect your system and organization based on the risk levels you identified during categorization. The goal is to transform your risk assessment into an actionable security plan.
Here’s what your business should do at this stage:
- Select and tailor control baselines
- Designate controls as system-specific, hybrid, or common
- Allocate controls to specific system components
- Develop and continuously monitor system-level strategies
- Review and approve security and privacy plans that reflect the control selection, designation, and allocation.
4) Implement
Implementation is when you actually deploy the controls outlined in your security and privacy plans throughout your system and organization. You can also update your security and privacy plans to reflect controls as they're actually implemented rather than as originally designed, ensuring everyone knows what protections are active and how they function in your specific environment.
5) Assess
Assessment determines whether your controls are implemented correctly, operating as intended, and producing the desired outcomes for meeting security and privacy requirements.
During assessment, your organization…
- Selects an assessor or assessment team
- Develops security and privacy assessment plans
- Reviews and approves assessment plans
- Performs control assessments in accordance with assessment plans
- Develops security and privacy assessment reports
- Takes remediation actions to address deficiencies in controls
- Updates security and privacy plans to reflect control implementation changes based on assessments and remediation actions
- Develops a plan of action and milestones
This process aims to create a roadmap for closing any security gaps discovered during testing.
6) Authorize
Authorization provides accountability by requiring a senior official to determine whether the security and privacy risk from operating a system or using common controls is acceptable to your organization.
During the authorization process your business should create an authorization package that includes an executive summary, system security and privacy plan, assessment reports, and plan of action and milestones.
Leadership then renders risk determination, provides risk responses, and approves or denies authorization for the system or common controls.
7) Monitor
Monitoring maintains ongoing awareness about your security and privacy posture to support continuous risk management decisions. The goal here is to:
- Track the system and environment in accordance with your monitoring strategy
- Perform ongoing assessments of control effectiveness
- Analyze and respond to monitoring outputs
- Maintain a process for reporting security and privacy posture to management
- Conduct ongoing authorizations using results of monitoring activities
What's The Best Way To Manage Your Social Media's Security?
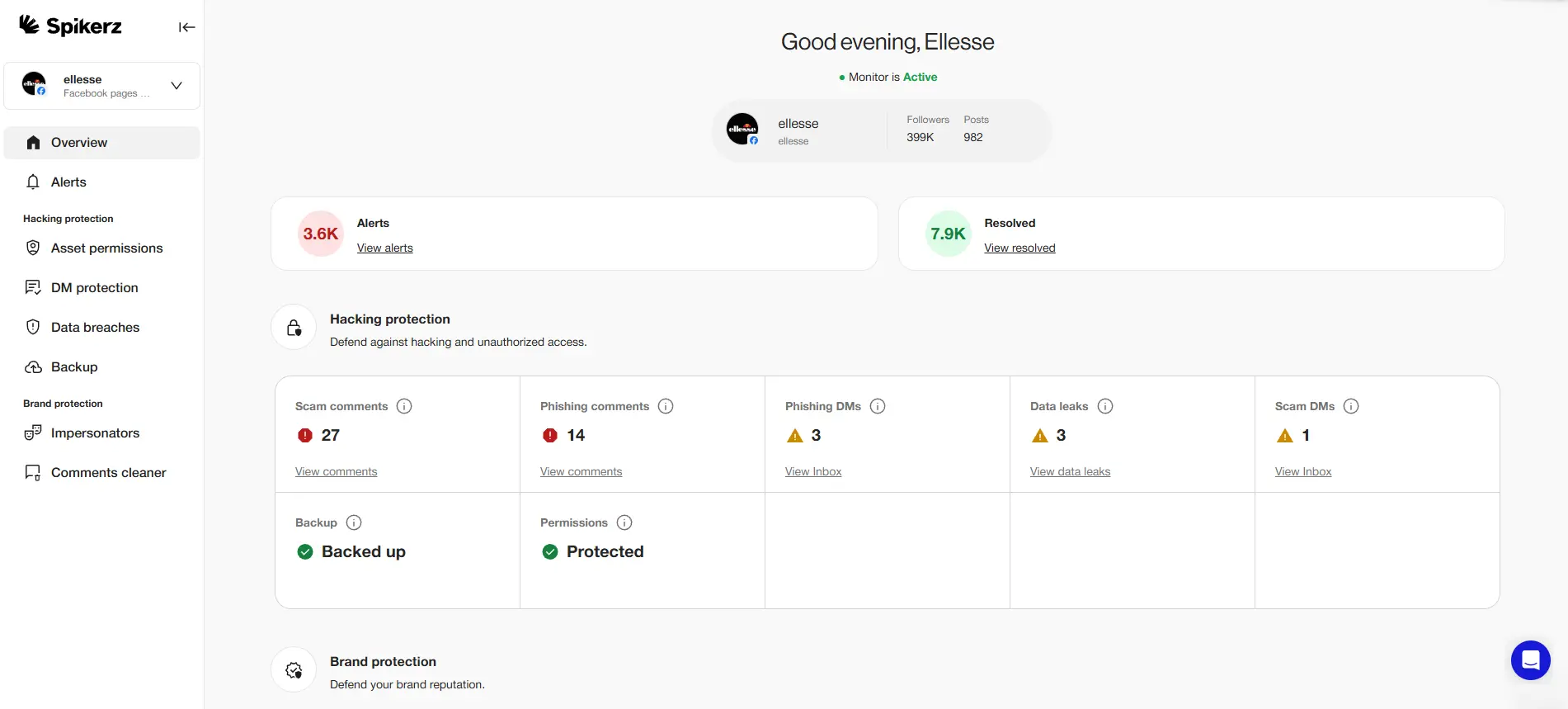
The best way to reduce your attack surface and improve your security is to use a social media security tool like Spikerz. It protects brands against hacking, phishing attempts, spam comments, impersonation, and manages user access across your social media presence.
Here's how each layer of protection works:
- Hacking Protection: Continuous monitoring detects suspicious login attempts, unauthorized access patterns, and credential theft before attackers can compromise your accounts. When abnormal activity is detected, the system alerts you immediately and automatically implements protective measures.
- Phishing Detection: Advanced algorithms scan messages and interactions for phishing attempts that try to steal your credentials or trick your team into revealing sensitive information. The system identifies and blocks these attacks across direct messages and comments.
- Comment Moderation: Automated content analysis removes spam, malicious links, and inappropriate comments from your posts before they damage your brand reputation. The best part is, the system learns your preferences and adapts its filtering to match your community standards.
- Impersonation Takedown: Real-time monitoring identifies fake accounts impersonating your brand across platforms and provides tools to report and remove them quickly.
- User Access Management: Centralized control over who can access your accounts, what permissions they have, and when those permissions expire. The system enables role-based access control and provides a dashboard that sheds light on all activity for easy audits.
Listen, your social media accounts are too valuable to leave vulnerable. Every day you wait is another day cybercriminals have to study your defenses, profile your team, and plan their attack.
The choice is simple: protect your brand before disaster strikes, or explain to stakeholders why you didn't take basic security measures.
Book a demo and see how Spikerz transforms your social media from a liability into a secure asset that drives business growth.
Conclusion
The seven-step NIST framework we shared provides a proven path for regulated businesses to identify vulnerabilities, implement controls, and maintain a strong security posture as threats evolve. But frameworks alone won't protect you, you need specialized tools that address the unique vulnerabilities in each part of your digital infrastructure.
That’s why you should use specialized tools to reduce your social media’s attack surface. The businesses that thrive are those that treat security seriously. Every hour your accounts remain unprotected is an hour cybercriminals spend mapping your weaknesses and planning their approach.
So go ahead and take control of your cyber risk management starting with your most vulnerable channels.

