My Instagram Account was Hacked. How can I get it back?
If your Instagram account has been hacked, you're not alone. Thousands of people face this issue daily, and it's essential to take swift action to regain control of your account and safeguard your digital assets. In this comprehensive guide, we will walk you through the process of recovering your hacked Instagram account step by step, with insights from our cybersecurity experts. Let's get started.
After extensive experience assisting countless individuals in their quests to recover hijacked social media accounts, our team of cybersecurity experts is excited to provide you with an updated guide on what actions to take when your Instagram (IG) account falls victim to hacking:
1. Protect Your Inner Circle
Hackers are quick and crafty. They'll use your identity to target your friends and family next. If you haven't done it already, share Spikerz with them. It's easier to keep a hacker out in the first place than to kick them out later.
2. Safeguard Your Valuables
Your Instagram account isn't the only thing at risk when it gets hacked. Think of it like a domino effect – your other accounts like email, bank, credit cards, and even your crypto wallet could be in danger. You've got to act fast to protect yourself from more harm. This could be as simple as changing your passwords for your other accounts or adding an extra layer of security with Two Factor Authentication (2FA).
3. Account Recovery Takes Time
Now that you've secured your other accounts, take a deep breath and follow the guidance from our cybersecurity experts. We've got your back and will guide you through the necessary steps to regain control. We've learned these methods from helping hundreds of folks just like you recover their social media accounts.
4. Activate 24/7 Online Account Protection & Insurance
Once you've recovered your account or created a new one, don't drop your guard. Hacked accounts are like magnets for future attacks. Protect yourself with constant 24/7 monitoring for your online accounts.
And the best part? You can make all of this happen with our user-friendly customized app! Just download Spikerz and follow our simple instructions to safeguard your digital life.
What are Instagram Hacks?
In today's landscape of Instagram hacking, it's essential to understand that hackers aren't exclusively targeting the accounts of celebrities and public figures; they're after ordinary individuals as well. But why are they so interested in your account, and why does reaching Instagram support seem like an arduous task?
In a nutshell, most hackers exploit Instagram accounts for financial gain. They capitalize on the trust your followers place in your name, making it easier for them to disseminate scams, propaganda, or spam. Additionally, hackers often prey on the anxiety and desperation you might feel when locked out of your account, manipulating you into sending substantial sums of money in exchange for the promise of account recovery. We've summed up the main ways for you and you are welcome to read more about their tricks HERE.

The Usual Instagram Scam Methods
- Phishing Messages: These deceptive messages can arrive via email, text, DMs, or other channels. Always double-check the sender's phone number or email address. These messages often trick you into verifying something by clicking on a suspicious link, redirecting you to a fraudulent website. You might be asked to provide your Instagram login details, security codes, or even sensitive information like your bank and credit card credentials. If the sender seems unfamiliar or the message raises suspicion, it's safest to delete it. When in doubt, consult Spikerz; our Experts are ready to assist.
- Fake Investment Opportunities: Have you ever come across posts promising enormous profits with minimal investment, such as through Venmo, CashApp, or Bitcoin advertisements? If it sounds too good to be true, it usually is. Exercise caution and skepticism.
- Giveaways: Some scams lure you into participating in giveaways, tempting you with fabulous prizes. However, to claim your winnings, you might be required to provide personal information or make payments. Be wary of such offers.
- Brand Collaboration Requests: Scammers often pose as "new, trendy" brands willing to pay you for promoting their products. They request your financial information, ostensibly for sending you a paycheck. In reality, they aim to breach your bank account. Be cautious and verify the legitimacy of such offers.
- Bogus Job Offers: Scammers seek personal information during their fake job interviews or hiring processes. They may ask for your home address, driver's license details, or banking credentials. Be extremely cautious when sharing sensitive information with potential employers.
- Exposed Passwords: One significant risk arises from compromised passwords. Millions of passwords are traded on the dark web daily, sometimes even for free. If your password is among them, there's no way to erase it from the dark web. However, you can render your old password obsolete by simply changing it regularly.
Stay Calm and Collected
Facing a hacked Instagram account can be distressing, but it's crucial to maintain a clear mind as you embark on the recovery process. Take a few deep breaths and remember that a hacked account isn't the end of the world. Recovering your account will take time, so it's important to set realistic expectations from the outset. There's no magical instant solution to retrieve your account, so be cautious of anyone or any services claiming to offer a quick fix for a hefty fee.
If you have any questions or concerns, don't hesitate to reach out to Spikerz. Online security should not be daunting.
Share Your Experience for Others to Learn
Let's be frank – not every Instagram recovery story ends happily. However, one of the most valuable things you can do is educate those around you. Share your experience to prevent others from falling victim to the same fate. If your account has been compromised, inform your followers immediately to mitigate any further damage. Treat this unfortunate incident as a learning opportunity, and elevate your awareness of cybersecurity. Remember, Instagram hacks are troublesome, but the consequences can be far worse if your primary email address or bank account is compromised.
Preventing your Instagram account from being hacked
You can adopt several proactive measures to safeguard your Instagram account from being hacked in the first place. While it might be a bit late for prevention for most of you reading this, it's still essential to bear these tips in mind, especially after recovering your account or creating a new one.
1. Enable two-factor authentication (2FA)
You can do this directly from your IG account settings. If you already have 2FA activated but you selected WhatsApp or SMS codes, switch the delivery method to a third-party authentication app in order to prevent the hackers from intercepting the recovery code. You can learn more about 2FA Here and follow these instructions:
- Settings -> Account Center -> Password and Security -> Two-Factor Authentication
.png)
2. Create a new strong and safe Password
If your passwords were leaked to the dark web, an unrelated event may have put your IG account at risk. It's important to use a unique password for every account rather than generic passwords that hackers can crack.
Read more about password security HERE and follow the instructions:
- Settings -> Account Center -> Password and Security -> Change Password
.png)
3. Enable backup coded
These can only be downloaded or written down, so a hacker should never be able to access them. Backup codes are automatically generated when you enable 2FA, so be sure to save them in a safe place and follow these instructions:
- Settings -> Account Center -> Password and Security -> Two-Factor Authentication -> Choose you account -> Additional methods -> Backup Codes
.png)
4. Monitor and check other devices/locations where you account is logged into
If you ever see a location or a device that you don't recognize, REMOVE IT IMMEDIATELY! Unrecognized devices can mean that someone else has access to your account. In this case, you should immediately change password and activate 2FA before it's too late and follow these instructions:
- Settings -> Account Center -> Password and Security ->Where you're logged in

5. Monitor and check third-party applications
Regularly check on which applications have been granted access to your Instagram account. Some third-party tools are riskier than others (like follower/unfollower monitoring apps), and NOT NECESSARY to maintain an IG account. If you keep any applications linked, you'll want to keep an eye out for any big data breaches that may affect you. Or these apps could be scams to begin with. To check follow these instructions:
- Settings -> Website permissions -> Apps and websites
.png)
- Don't forget to secure your email account associated with your Instagram account
This might be obvious, but if a hacker has access to your email, they can easily hack and steal any account associated with it. Be sure to enable 2FA and change your password so that it is both strong and different from any other passwords you use.
Join Spikerz's Social Media Security Services today. As we've emphasized earlier, time is of the essence when you're facing an attack. Our team of cybersecurity experts prioritizes your security by first fortifying all your digital assets before hackers can exploit them. Then, we guide you in implementing the aforementioned security measures to recover your account and ensure it remains safeguarded.
Our methods have successfully aided numerous individuals in reclaiming their accounts. On average, the recovery process typically spans 1-2 weeks, a small investment of time considering the potential risks of re-hacking. To bolster your protection, activate round-the-clock account monitoring and identity theft insurance. These precautions are essential for long-term security.
Explore Spikerz's comprehensive solutions, including Online Account Protection and Credit Monitoring features, designed to shield your most critical assets such as your email, other social media accounts, and your finances. Your peace of mind is our top priority.
Recovery Guide of Your Hacked Instagram Account
The specific recovery procedure can vary from one person to another because Instagram continually experiments with various features and methods, often contingent on your device type and app version. It's entirely possible that you won't encounter identical recovery options as someone else, at least not at this moment. Therefore, it's crucial to bear this in mind and maintain perseverance when seeking to reclaim a compromised account.
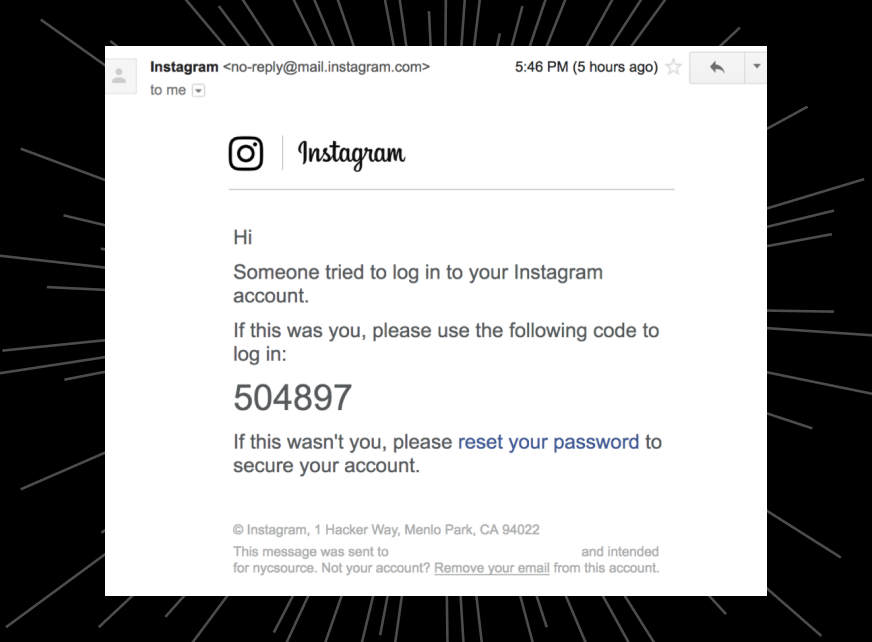
Step 1: Security Email Check
Initiate your recovery process by thoroughly checking your email inbox for correspondence from Instagram. This email serves as an early warning system, notifying you of suspicious activities such as new device logins or changes to your email address. Follow the instructions provided in this email promptly to reset your password and fortify the security of your account.
- Check your inbox for an email from Instagram.
- Instagram sends this email if they detect suspicious activity like new device logins or email changes.
- Use the email and the instructions sent to reset your password and secure your account.
Step 2: Request a Login Link
For accounts with unchanged backup contact information, the next step involves requesting a password reset link from Instagram. Navigate to "Get Help Logging in" on Android or "Forgot Password" on iPhone, through the web, or within the app. This familiar process is akin to resetting a forgotten password and serves as an initial attempt to regain control.
- If your backup contact info is unchanged:
- Request a password reset link from Instagram.
- Select "Get Help Logging in" on Android or "Forgot Password" on iPhone, via web or app.
- This process is similar to resetting your password when forgotten.
.png)
Step 3: Video Selfie Recovery
In cases where the hacker has activated Two-Factor Authentication (2FA) on your account, the Video Selfie Recovery option becomes crucial. Access this feature through your Instagram app on a recognized device. Follow the prompts, which may include obtaining a security code and submitting a video selfie that aligns with your posted photos. Persistence is key, and consider resubmitting the video selfie if the initial attempt proves unsuccessful.
For accounts with Two-Factor Authentication (2FA) set up by the hacker, you may need to submit a video selfie, turning your head to match your posted photos:
Access this option through your IG app on a recognized device:
- Find your current username, even if altered by the hacker.
- Click "Forgot Password?"
- Tap "NEXT" to reveal the hacker's contact info (if available).
- If not visible, choose "Can't Reset Your Password?" or "Try Another Way."
- Follow prompts to receive a security code.
- Enter the code and complete a form, providing reliable contact info.
- Take note of the confirmation screen, and check for a confirmation email.
- This method is effective if your Instagram account contains many photos of yourself.
- If denied, consider submitting a new Video Selfie every few days until you receive a response.
Step 4: Support Assistance
When traditional recovery methods prove insufficient, opt for "Try Another Way" and select "Get Support" from the menu. Provide concise answers and a reliable email address for recovery instructions. Instagram's support team can offer tailored assistance, serving as a bridge when standard procedures fall short.
If you can't retrieve your contact info or security code:
- Select "Try Another Way" and choose "Get Support" from the menu.
- Follow the instructions provided, giving quick answers and a reliable email address for recovery instructions.
Step 5: No Photos of Yourself
For accounts lacking identifiable photos, choose the option acknowledging the absence of personal images. Follow the emailed instructions, which may involve providing initial email addresses, phone numbers, and device details. This pathway recognizes diverse account content and offers recovery alternatives for those without a significant presence in photos.
If you lack photos of yourself on your account:
- Select "No, I don't have photos of myself" and follow email instructions.
- Instructions may include providing your initial email address or phone number and device type.
Step 6: Selfie Photo with a Hand-Written Code
Some users may be directed to a specialized form, requesting a selfie photo holding a hand-written code provided by Instagram. This, coupled with additional account details, contributes to a comprehensive recovery effort. Patience is paramount as responses to this method may take 2-3 weeks.
Some users may be directed to a different form without the option of a Video Selfie:
- This form may request account details and ask for a photo of yourself holding a hand-written code provided by Instagram, along with your full name and username.
- After submission, wait for a response, which can take up to 2-3 weeks.
- Remember, recovery paths may vary, and persistence is key to reclaiming your hacked Instagram account.
Step 7: Submit Instagram's Hacked Account Form
In cases where previous attempts prove futile, submit Instagram's Hacked Account Form via this link. Select "My Account Got Hacked" as the reason and provide relevant information, such as the username, phone number, or email. If the hacker altered this information, diligently search for the new username and follow the provided instructions.
- Select the reason "My Account Got Hacked"
.png)
- Type in the Username, Phone number or email, if not changed by hacker
- If changed by hacker, try to find the new username the hacker changed to
- Follow the instructions
Step 8: Report an Impersonation
- Access the reporting process by clicking on this link: https://help.instagram.com/contact/636276399721841
- Choose the option: "Someone is impersonating me or my friend.
- Confirm that you are the person being impersonated by selecting: "Yes, I am the person being impersonated."
- Attach a clear selfie of your actual face along with your ID in the same photo to verify your identity.
- In the "Additional Info" section at the bottom, explain the situation thoroughly.
- Include as much detail as possible to prove that the account in question is genuinely yours.
- For a quicker response, select: "Someone created an account pretending to be me or a friend."
- Again, confirm that you are the person being impersonated by selecting: "Yes, I am the person being impersonated."
- Ensure that all fields are accurately filled out to improve the chances of Instagram addressing your report promptly.
.png)
Remember, each recovery journey is unique. Persistence, adaptability, and a systematic approach will empower you to navigate the complexities of Instagram account recovery successfully.
Spikerz - Your Guardian Against Social Media Threats
In the dynamic landscape of social media, securing your online presence is no longer an option but a necessity. Introducing Spikerz, a comprehensive solution designed to be your unwavering defender against a myriad of social media threats.
- Phishing Protection:Spikerz employs cutting-edge AI technology to counteract sophisticated phishing attacks. Our AI-powered phishing detector meticulously analyzes links, senders, and content within social platform chats, identifying and neutralizing potential phishing threats before they can compromise your account.
- Lockout Protocol:In the unfortunate event of a phishing attempt, Spikerz initiates a real-time lockout protocol. This feature acts swiftly, severing any suspicious login activities and enhancing security measures to ensure the integrity of your account remains intact.
- Data Protection:At Spikerz, we understand the value of your content. Our system ensures continuous backup of all user content, including messages, posts, comments, and stories. This ensures that even in the rare scenario of a successful breach, no valuable data is lost, facilitating a seamless recovery process.
- Bot Protection:Sophisticated AI bots generating vast amounts of content pose a significant threat. Spikerz employs a state-of-the-art deep learning model crafted to identify and neutralize these advanced bots, preserving the authenticity of your online presence.
- Comment Protection:Guarding your online space from comment spam is paramount. Spikerz provides a robust tool that consistently monitors and auto-removes harmful comments from bots, hackers, or competitors, fostering a secure environment for your business and customers.
- Guidelines Protection:Spikerz understands the importance of compliance. Our AI algorithm proactively scans your content and activities, offering protection against potential rule violations that could lead to social media bans or suspensions, safeguarding your revenue streams.
- Impersonation Protection:Brand impersonation and customer fraud are on the rise. Spikerz employs advanced AI to detect and eliminate fraudulent impersonators, preserving the integrity of your brand and ensuring your audience engages with the authentic you.
- Spam Protection:Competitor-driven spam attacks can hinder genuine client interactions. Spikerz employs real-time spam detection and blocking mechanisms to protect your account from flooding, maintaining a positive and authentic engagement experience.
With Spikerz, you're not just securing your social media accounts; you're investing in a robust defense system that adapts and evolves to stay ahead of emerging threats. Join the Spikerz family today and fortify your digital presence against the ever-evolving landscape of social media threats. Click [here](insert Spikerz landing page link) to embark on a secure online journey with Spikerz!
Join Spikerz today and start securing your social media account !

